Dashboard
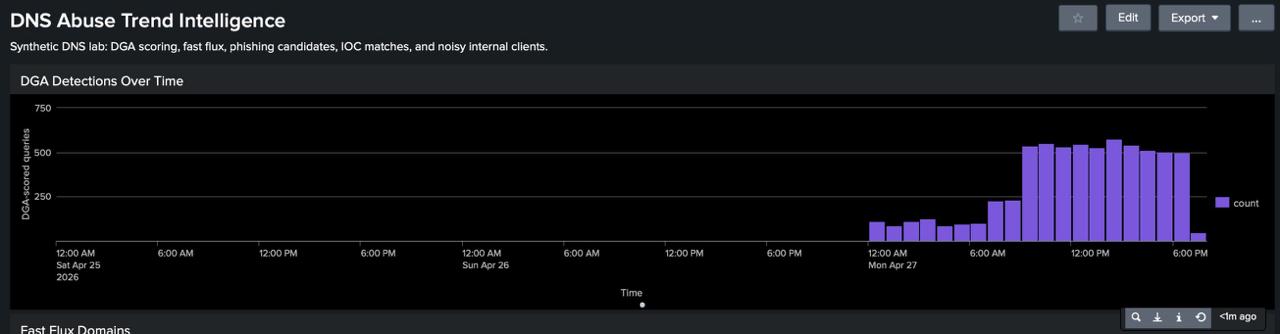
DGA DETECTIONS OVER TIME
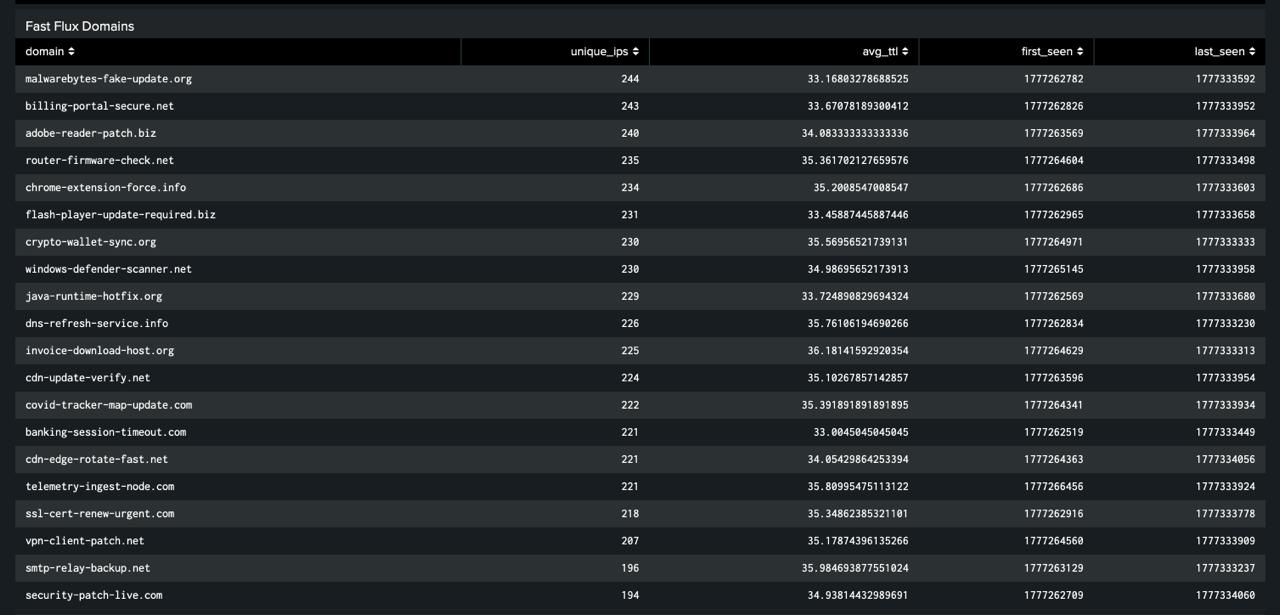
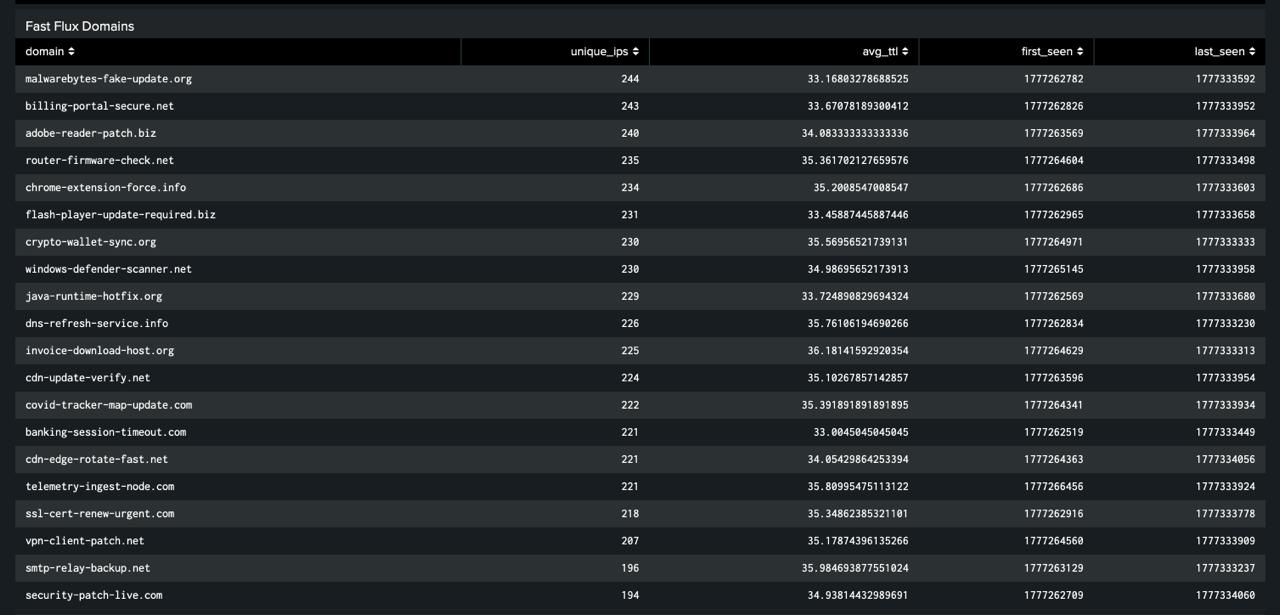
FAST FLUX DOMAINS
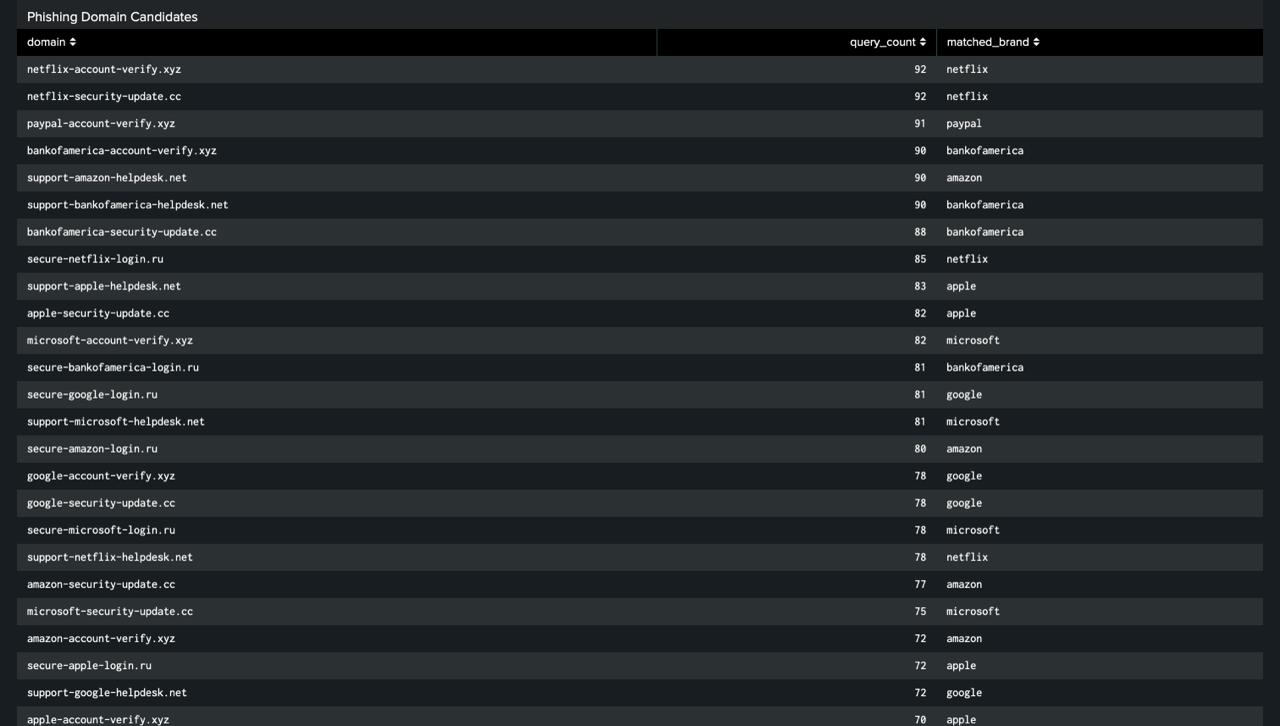
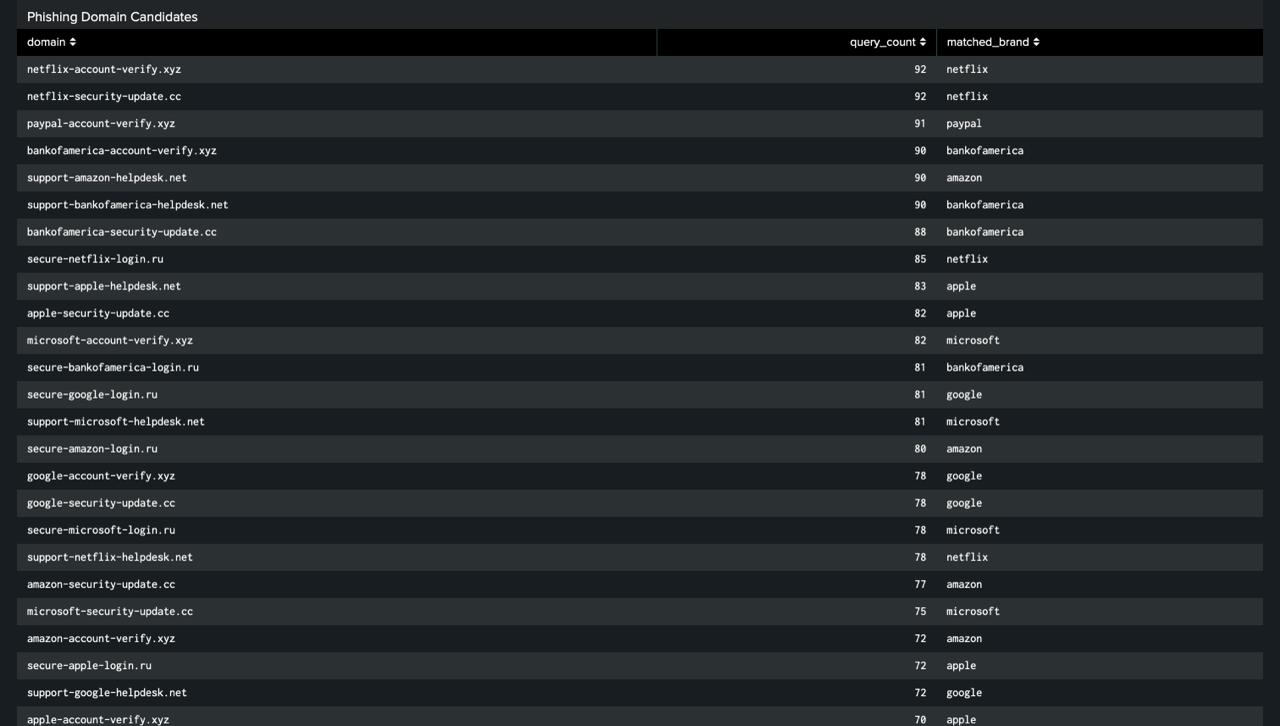
PHISHING CANDIDATES
Synthetic DNS log pipeline → behavioral detections → live IOC enrichment → Splunk dashboard
End-to-end DNS threat detection pipeline built to demonstrate detection engineering and SIEM development in a Security Operations context. Generates high-volume synthetic DNS telemetry, runs behavioral detections across three threat categories, enriches matches against live open-source threat intelligence, and surfaces everything in a five-panel Splunk dashboard.
| Feed | Provider | IOCs | Type |
|---|---|---|---|
| URLhaus | abuse.ch | 30,338 | Malware distribution URLs |
| ThreatFox | abuse.ch | 948 | C2 indicators, malware IOCs |
| AlienVault OTX | AT&T Cybersecurity | 700 | Community threat pulses |
| Panel | Function | Category |
|---|---|---|
| DGA Detections Over Time | Detect | DE.AE — Anomalies & Events |
| Fast Flux Domains | Detect | DE.CM — Continuous Monitoring |
| Phishing Candidates | Detect | DE.CM — Continuous Monitoring |
| IOC Matches | Identify | ID.RA — Risk Assessment |
| Top Suspicious Clients | Respond | RS.AN — Analysis |